Vulnerability Findings
Retrieves vulnerability data and associated metadata for assets from Tenable, including details like CVE identifiers, CVSS scores, descriptions, solution information, and affected systems.
Sync Type: Incremental
Requirements
- Log in to Tenable.io and go to the Create a service account page.
- Enter
Monad Serviceas the name. - Fill out the rest of the service account fields using your organization's usual process.
- Set the Role to
Scan Managerand click Finish.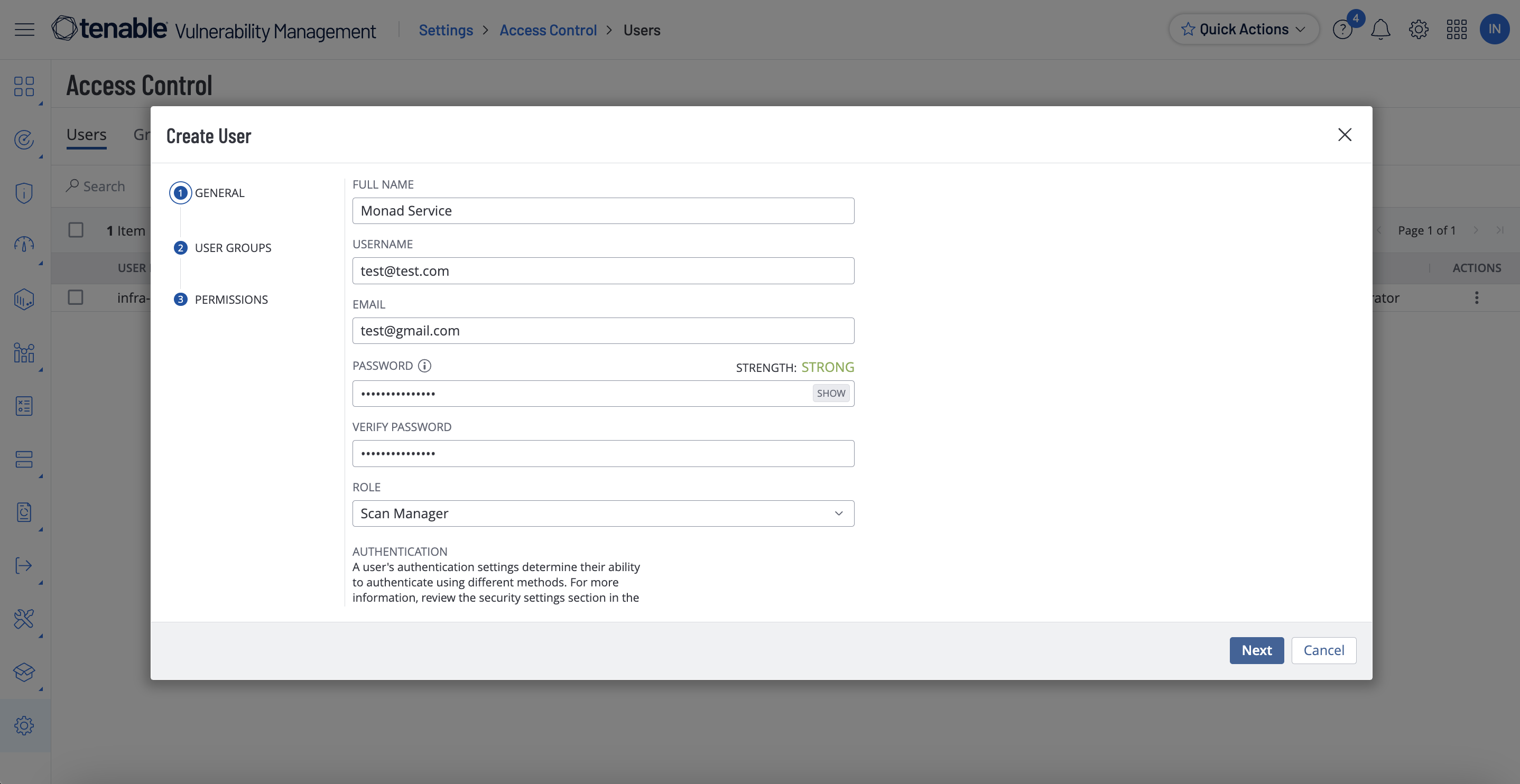
- Click the new service user and select API Keys on the left.
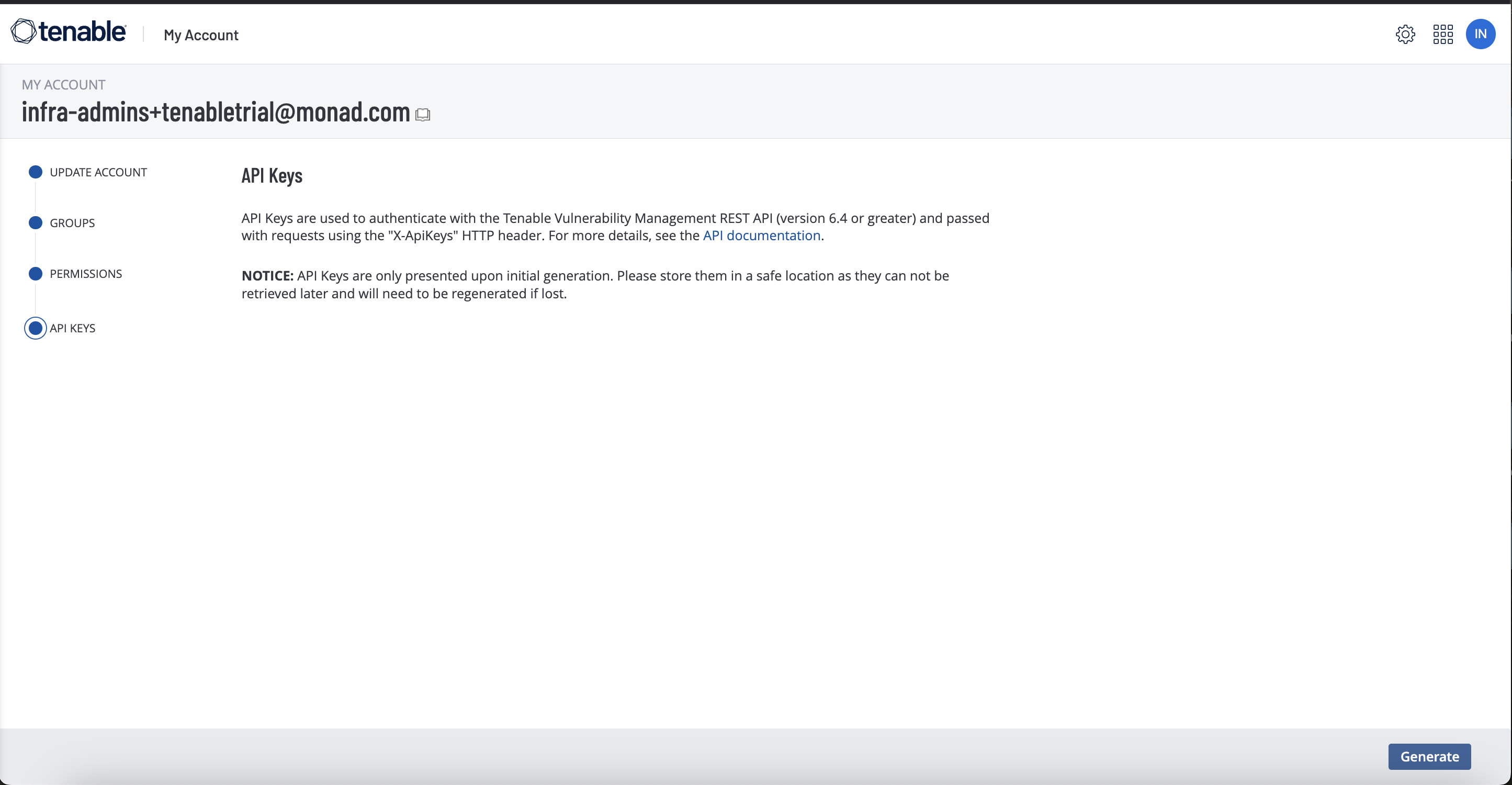
- Copy the access key and secret key. You'll need them when you set up the Monad connector.
Details
Monad uses the since filter on the API and no others to determine which vulnerabilities to export. This field is updated every time the export is successful with the last export initiation time. as per the tenable documentation linked above... If you do not include the state filter in your request(which we do not), the export includes data for OPEN and REOPENED vulnerabilities that were seen on or after the since date you specify, and FIXED vulnerabilities that were fixed on or after the since date you specify. This means if any vulnerabilities are updated beyond its state its updated data will not be included in the export.
Configuration
The following configuration defines the input parameters. Each field's specifications, such as type, requirements, and descriptions, are detailed below.
Settings
| Setting | Type | Required | Description |
|---|---|---|---|
| Backfill Start Time | string | No | The date to start fetching data from. If not specified, no past records will be fetched. |
Secrets
| Secret | Type | Required | Description |
|---|---|---|---|
| Access Key | string | Yes | Access Key for the Tenable API. This is required to authenticate requests. |
| Secret Key | string | Yes | Secret Key for the Tenable API. This is required to authenticate requests. |
OCSF Conversion
The following JQ transformation converts Tenable Vulnerability data to OCSF Version 1.0.0-rc.2 compliant format.
JQ Transformation
{
class_uid: 2002, #Vulnerability Finding
category_uid: 2, #Findings
type_uid: 200200, #Vulnerability Finding: Unknown
activity_id: 0, #Unknown
time: (.scan.started_at | gsub("\\.\\d+Z$"; "") | strptime("%Y-%m-%dT%H:%M:%S") | mktime),
severity_id: .severity_id,
metadata: {
version: "1.1.0",
product: {
vendor_name: "Tenable",
name: "Nessus"
}
},
raw_data: (. | tostring),
finding_info: {
title: .plugin.name,
uid: (.plugin.id | tostring),
last_seen_time: (.last_found | gsub("\\.\\d+Z$"; "") | strptime("%Y-%m-%dT%H:%M:%S") | mktime),
first_seen_time: (.first_found | gsub("\\.\\d+Z$"; "") | strptime("%Y-%m-%dT%H:%M:%S") | mktime)
},
vulnerabilities: [{
desc: .plugin.description,
name: .plugin.name,
uid: (.plugin.id | tostring),
cvss: {
version: "3.0",
vector: .plugin.cvss3_vector.raw,
base_score: .plugin.cvss3_base_score
},
remediation: {
desc: .plugin.solution
}
}]
}
OCSF Mapping Details
The JQ transformation converts Tenable Vulnerabilities to OCSF Version 1.0.0-rc.2 with the following key mappings:
Core Fields
- Class UID: Set to 2002 (Vulnerability Finding)
- Category UID: Set to 2 (Findings)
- Type UID: Set to 200200 (Vulnerability Finding: Unknown)
- Activity ID: Set to 0 (Unknown)
- Time: Extracted from the scan's
started_atfield- Strips milliseconds from the ISO timestamp
- Converts to Unix timestamp format
- Severity ID: Maps directly from the vulnerability's
severity_id
Finding Information
- Title: Maps from the plugin's name
- UID: Converts the plugin ID to string format
- Last Seen Time: Converts
last_foundtimestamp to Unix format - First Seen Time: Converts
first_foundtimestamp to Unix format
Vulnerability Details
- Description: Maps from plugin description
- Name: Maps from plugin name
- UID: Plugin ID in string format
- CVSS Information:
- Version: Set to "3.0"
- Vector: Maps from raw CVSS3 vector
- Base Score: Maps from CVSS3 base score
- Remediation: Maps solution information from plugin
Metadata
- Version: Set to "1.0.0-rc.2"
- Product:
- Vendor name: "Tenable"
- Name: "Nessus"
Customization
The transformation serves as a starting point and can be modified to accommodate specific requirements while maintaining OCSF compliance. The mapping prioritizes essential asset information and cloud provider detection while providing fallback values for optional fields.
Related Articles
- https://developer.tenable.com/reference/exports-vulns-download-chunk
- https://docs.tenable.com/vulnerability-management/Content/Settings/access-control/CreateAUserAccount.htm
- https://developer.tenable.com/reference/exports-vulns-request-export
- https://developer.tenable.com/reference/exports-vulns-export-status
- https://developer.tenable.com/reference/exports-vulns-download-chunk
Sample Record
{
"asset": {
"agent_uuid": "08b52ca9c8a44c0593d6b3f56235c291",
"device_type": "general-purpose",
"fqdn": "macbook-air.local",
"hostname": "John Miller -macbook-air-2.local",
"uuid": "41fb04af-6de3-49f5-9b76-6cd021f09333",
"ipv4": "172.240.152.101",
"ipv6": "fde7:ae64:a9bc:154d:46b:2b3a:1357:cffe",
"last_authenticated_results": "2025-08-11T23:46:44.387875Z",
"mac_address": "b2:21:5c:6b:8a:a0",
"netbios_name": "MacBook-Air",
"operating_system": [
"macOS 14.4.1"
],
"network_id": "00000000-0000-0000-0000-000000000000",
"tracked": true
},
"output": "\n Path : /Applications/Firefox.app\n Installed version : 82.0.3\n Fixed version : 122.0\n",
"plugin": {
"bid": [
189363
],
"checks_for_default_account": false,
"checks_for_malware": false,
"cpe": [
"cpe:/a:mozilla:firefox"
],
"cvss3_base_score": 8.8,
"cvss3_temporal_score": 7.7,
"cvss3_temporal_vector": {
"exploitability": "Unproven",
"remediation_level": "Official Fix",
"report_confidence": "Confirmed",
"raw": "E:U/RL:O/RC:C"
},
"cvss3_vector": {
"access_complexity": "Low",
"access_vector": "Network",
"availability_impact": "High",
"confidentiality_impact": "High",
"integrity_impact": "High",
"raw": "AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H"
},
"cvss_base_score": 10.0,
"cvss_temporal_score": 7.4,
"cvss_temporal_vector": {
"exploitability": "Unproven",
"remediation_level": "Official Fix",
"report_confidence": "Confirmed",
"raw": "E:U/RL:OF/RC:C"
},
"cvss_vector": {
"access_complexity": "Low",
"access_vector": "Network",
"authentication": "None required",
"availability_impact": "Complete",
"confidentiality_impact": "Complete",
"integrity_impact": "Complete",
"raw": "AV:N/AC:L/Au:N/C:C/I:C/A:C"
},
"description": "adipiscing pariatur ex proident laborum dolore consectetur consectetur aute incididunt officia aliquip consequat nisi qui eu nostrud commodo minim dolor aute dolore reprehenderit lorem proident dolore mollit in occaecat cillum laborum laborum dolor elit consequat aliquip dolor quis incididunt aute ullamco nulla adipiscing est nisi voluptate in officia laboris qui",
"exploit_available": false,
"exploit_framework_canvas": false,
"exploit_framework_core": false,
"exploit_framework_d2_elliot": false,
"exploit_framework_exploithub": false,
"exploit_framework_metasploit": false,
"exploitability_ease": "No known exploits are available",
"exploited_by_malware": false,
"exploited_by_nessus": false,
"family": "MacOS X Local Security Checks",
"family_id": 26,
"has_patch": true,
"id": 189363,
"in_the_news": false,
"name": "Mozilla Firefox < 122.0",
"patch_publication_date": "2025-08-11T23:46:44.38792Z",
"modification_date": "2025-08-11T23:46:44.387921Z",
"publication_date": "2025-08-11T23:46:44.387923Z",
"risk_factor": "critical",
"see_also": [
"https://www.mozilla.org/en-US/security/advisories/mfsa2024-01/"
],
"solution": "Upgrade to Mozilla Firefox version 122.0 or later.",
"stig_severity": "I",
"synopsis": "A web browser installed on the remote macOS or Mac OS X host is affected by multiple vulnerabilities.",
"unsupported_by_vendor": false,
"version": "1.7",
"vuln_publication_date": "2025-08-11T23:46:44.387924Z",
"xrefs": [
{
"type": "CVE",
"id": "2024-0741"
},
{
"type": "CVE",
"id": "2024-0742"
},
{
"type": "CVE",
"id": "2024-0743"
},
{
"type": "CVE",
"id": "2024-0744"
},
{
"type": "CVE",
"id": "2024-0745"
},
{
"type": "CVE",
"id": "2024-0746"
},
{
"type": "CVE",
"id": "2024-0747"
},
{
"type": "CVE",
"id": "2024-0748"
},
{
"type": "CVE",
"id": "2024-0749"
},
{
"type": "CVE",
"id": "2024-0750"
},
{
"type": "CVE",
"id": "2024-0751"
},
{
"type": "CVE",
"id": "2024-0752"
},
{
"type": "CVE",
"id": "2024-0753"
},
{
"type": "CVE",
"id": "2024-0754"
},
{
"type": "CVE",
"id": "2024-0755"
},
{
"type": "IAVA",
"id": "2024-A-0053-S"
},
{
"type": "IAVA",
"id": "2024-A-0174-S"
},
{
"type": "IAVA",
"id": "2024-A-0245-S"
}
],
"vpr": {
"score": 6.7,
"drivers": {
"age_of_vuln": {
"lower_bound": 61,
"upper_bound": 180
},
"exploit_code_maturity": "UNPROVEN",
"cvss_impact_score_predicted": false,
"cvss3_impact_score": 5.9,
"threat_intensity_last28": "VERY_LOW",
"threat_sources_last28": [
"No recorded events"
],
"product_coverage": "MEDIUM"
},
"updated": "2025-08-11T23:46:44.387927Z"
},
"cve": [
"CVE-2024-0741",
"CVE-2024-0742",
"CVE-2024-0743",
"CVE-2024-0744",
"CVE-2024-0745",
"CVE-2024-0746",
"CVE-2024-0747",
"CVE-2024-0748",
"CVE-2024-0749",
"CVE-2024-0750",
"CVE-2024-0751",
"CVE-2024-0752",
"CVE-2024-0753",
"CVE-2024-0754",
"CVE-2024-0755"
],
"type": "local"
},
"port": {
"port": 0,
"protocol": "TCP"
},
"scan": {
"schedule_uuid": "template-382cf2db-8da2-d050-0e26-77fcb89a68a313c4f6712eaeab02",
"started_at": "2025-08-11T23:46:44.387928Z",
"uuid": "8fe8810b-e7cb-ef75-6046-25b405133937"
},
"severity": " Low",
"severity_id": "2",
"severity_default_id": 4,
"severity_modification_type": "NONE",
"first_found": "2025-08-11T23:46:44.387976Z",
"last_found": "2025-08-11T23:46:44.387978Z",
"state": "OPEN",
"indexed": "2024-07-08T17:17:08.504884Z",
"source": "AGENT"
}